Compliance with biometric solutions is necessary in the era of fast and secure technology. People are now more inclined towards using the latest technology because it simplifies the operations of individuals. Scammers are trying innovative ways to hack the customer’s account. To control fraudulent activities, compliance with the face ID check is essential. These tools are used for security measures, verifying the client’s identity. The cybersecurity market is expected to reach 538.3$ billion by 2030. Let’s explore photo identity verification and how it is better than conventional means.
Table of Contents
Understanding of Photo Identity Verification
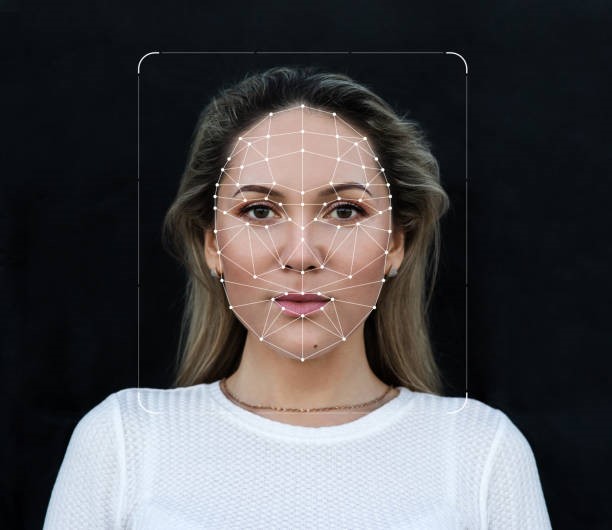
Face verification is a solution of the biometric system; the scanner performs the verification to certify that the customer profile is legitimate. Onboarding clients after their authentication can reduce their risk rate. By doing this, companies can safeguard their data. Moreover, to execute this process online; the scanner verifies the customer’s face, finger, voice, or eye and compares it to the previously stored data. Hence, the system grants access to the clients whose records are matched, and the verification of the suspicious persons is rejected.
Machine learning tools are used to verify the profile of the client. These solutions do not commit any mistakes, and they record the exact data. The scanners can even find a face from the crowd, images, or videos. The system forms the templates that are readable by the solution in the back-end.
Anit Spoofing Techniques for Photo ID Verification
- The biometric solutions are accurate and reliable but have some drawbacks. The hackers are using innovative ways to dodge the scanner. They present the paper paper-based image to get access. For this purpose, face recognition deep learning is used; it controls all such issues and properly certifies that the actual user is trying to log in to the system. For this purpose, the system checks the skin texture of the user, and the paper-based image does not contain any blemishes. Therefore, if the hacker performs spoofing attacks, such issues can be easily detected.
- The screen also asks some security questions, which only authentic clients can answer, such as the mother’s maiden name and the residential address. So, if the scammer is presenting fake pictures or videos to get access, such activity is immediately detected. These scanners are also trained to spot presentation attacks.
How is Facial Recognition Better than Traditional Verifications?
- In the conventional means, the employees must first collect the records, gather them, and then verify them. The company’s staff must perform all the processes, which takes time. The organizations have to hire a large number of people for this verification. Therefore, their expenditures are increased due to it. Other than this, they also have to monitor their customer’s activity, and managing all such operations is complex. The latest verifications use face-check techniques to onboard the users and check their profiles. The artificial intelligence tools are experts trained to verify the users. These solutions do not commit any mistakes, and companies can entirely rely on them.
- The machine learning tools swiftly onboard the users and save and monitor their data. Businesses must hold a comprehensive record of their clients to reduce the probability of fraudulent activities. They must be aware of their customers’ source of income to control money laundering cases. Organizations that do not take such actions have to face many complications, as their brand image is affected, and they also lose their potential clients due to it. Other than this, the companies have to safeguard the user’s credentials. The face recognition algorithms are robust, and it is impossible to hack them. Therefore, the clients also prefer the brand that facilitates them to their maximum.
- Face check ID is showing its wonders in almost every industrial sector. The banks especially onboard their customers through the biometric solution. They create their digital accounts through these tools. In addition to this, they also monitor their activities so that the company can segregate them as high-risk or low-risk users. The businesses then build relationships with their users accordingly.
Conclusion
The face check ID increases the surveillance of the companies, and it allows only valid users to interact with the company. The biometric solutions onboard the customers, verify their profiles and observe their activities. Organizations can boost their success rate through these tools, as their miscellaneous expenses are reduced, and they can invest this amount in any other task. The advanced tools detect spoofing, 3D, and presentation attacks. In this way, the companies can secure them against the fraudulent cases. The integration of these technologies aids in compliance with the company’s instructions.
Related Post: How to Use Chat GPT as a Learning Tool